NSA Contributes Security Tools For Puppet
IT automation specialist Puppet Labs has announced a new partner: The U.S. National Security Agency. Puppet Labs said Friday (June 19) that NSA is releasing to the open source ...Full Article
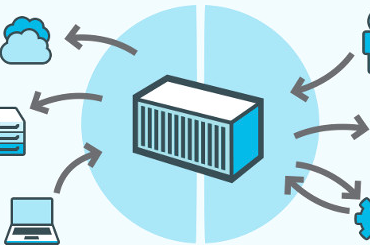
Red Hat Survey Highlights Container Certification
Production deployment of Linux application containers may not be meeting expectations, but there is no shortage of industry surveys attempting to pinpoint barriers to adoption. The latest released on ...Full Article
Bring Shadow IT Out of the Dark, Gartner Tells Tech
Mention shadow IT to many technology professionals and they'll shudder before trading war stories. But to empower their organizations to innovate, grow, and succeed, IT departments must embrace and manage this ...Full Article
To Improve Cybersecurity, Fire Some CEOs
Despite the amazing number of cybersecurity breaches, so far the Target CEO appears to have been the only one to pay the price. While we hear some calls for ...Full Article
Ex-Baidu Researcher Ren Wu Denies Wrongdoing
Dr. Ren Wu vigorously denies the charges of cheating that led Baidu to reportedly fire the head of its Heterogeneous Computing team after the Chinese search engine developer's supercomputer team ...Full Article
RAND Corp: Manage Security Like a Business
Organizations must figure out a better way to manage cybersecurity like a business, using metrics to determine the relative return on investment (RROI), and constantly evaluating the lifecycle and ...Full Article
Government Labs Give Enterprises a Supercomputing Boost
International conglomerates, tech startups, and SMBs can tap into the federal government's investments in supercomputers and expertise through a series of programs operated by several of the nation's leading ...Full Article
How to Avoid Being a Hacker Victim
Following in the wake of the recently publicized attacks on government databases and systems, all CIOs and chief security officers should assume their own organizations could be next and ...Full Article
Federal State of Cyber Insecurity: New Day, New Breach?
When the United States government accused China of hacking the Office of Personnel Management and gaining access to the records of 4 million current and former federal employees, it ...Full Article
Asset Disposal: Old Computers Bring New Security Worries
In an age where organizations are consolidating datacenters, embracing cloud, and data infiltrates everything via the Internet of Things (IoT), enterprises increasingly must consider how to securely, legally, and ...Full Article