Are Breaches Killing Flash?

Mozilla added the Flash Player Plugin to its roster of blocked add-ons, after yet another security alert from developer Adobe and following a public call for the end of Flash by a Facebook executive earlier in the week.
While developers, enterprises, and end users figure out how to deal with this particular security risk, the situation demonstrates inherent weaknesses in the entire system, Jerome Segura, senior security researcher at Malwarebytes Labs, research arm of the anti-malware company, told Enterprise Technology. "The bigger picture is that there are more zero days than we really imagined before and even relatively small groups like Hacking Team are able to produce them on a regular basis. We also need to think beyond Flash, and although measures such as removing it completely are effective and responsible, they may also be short sighted," he said. "If a Chrome zero-day was released tomorrow, would we tell everyone to never use that browser again? We need to adopt our security posture to face the reality brought by these new threats, regardless of what pieces of software are affected."
On July 14, Adobe released new security updates for Adobe Flash Player for Windows, Macintosh, and Linux. "These updates address critical vulnerabilities that could potentially allow an attacker to take control of the affected system. Adobe is aware of reports that exploits targeting these vulnerabilities have been published publicly," the developer said on its website.
Adobe is pursuing additional security initiatives to strengthen the software, the company said.
"There are extensive efforts underway internally, in addition to our work with the security community and our counterparts in other organizations, to help keep our products and our users safe," Wiebke Lips, senior manager of Adobe's corporate communications, told The Register.
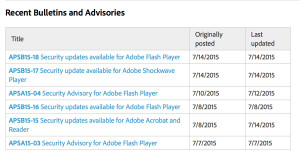
Today's update follows earlier patches for the same product on July 10, 8, and 7, plus patches on July 14 for Shockwave and July 8 for Acrobat and Reader. Flash Player underwent two patches in June.
But Adobe's moves have not assuaged some developers' fears.
"When Mozilla becomes aware of add-ons, plugins, or other third-party software that seriously compromises Firefox security, stability, or performance and meets certain criteria, the software may be blocked from general use," Mozilla said in a post. "… Attackers can use the security flaws in Flash to run malicious software on your computer and gain access to your system."
To access Flash, users must manually change their plugin setting, Mozilla said. Google already disables outdated plugins, noted Malwarebytes Labs' Segura. The Flash situation is another argument for a layered approach to security, he noted.
"The Flash Player has been heavily targeted in online attacks and without a doubt there will be more in the near future. Deciding to uninstall or put Flash in 'click to play mode' is a decision that IT admins will have to make," said Segura. "Regardless, a layered approach to defending your assets remains key, and in light of recent zero-days that affect not only Flash but other pieces of software, anti-exploit mitigation software has proven to be necessary."
Concern about Flash security grew in the wake of the Hacking Team breach, when hackers infiltrated the Italian developer of surveillance software and released more than 400 gigabytes of data. Customers, which include the FBI and reportedly potentially were set to expand into Miami-Dade police, included regions with a legacy of human-rights complaints, such as Saudi Arabia, Sudan, and Ethiopia.
Hidden among the stolen data was a new Flash Player zero-day affecting Flash Player up to version 18.0.0.194.
"We first discovered the Flash zero-day hit at 3 PM PT and we believe it is the same as the one revealed in the Hacking Team hack, which we blogged about earlier today," wrote Segura in a company blog earlier this month. "This is one of the fastest documented case of an immediate weaponization in the wild, possibly thanks to the detailed instructions left by Hacking Team."
Malwarebytes' security software blocked the latest zero-day offensive, including in Firefox, the developer reported. Enterprises should ensure security software is current, experts recommended, and that it resolves these exploits. For its part, Adobe hopes to patch CVE-2015-5122 and CVE-2015-5123 holes today, the Register reported.
"There are Flash alternatives, and many popular video streaming sites now use HTML5 instead to render the content. We expect the trend to continue, although it might still be a few years before that happens everywhere. For people still using Flash in their browser, we strongly recommend using a dedicated browser for it," Segura said. "On top of that, using the right security tools that detect malicious Flash files is now made easy and very effective thanks to anti-exploit technology."
Related
Managing editor of Enterprise Technology. I've been covering tech and business for many years, for publications such as InformationWeek, Baseline Magazine, and Florida Today. A native Brit and longtime Yankees fan, I live with my husband, daughter, and two cats on the Space Coast in Florida.